What is CRTP?
CRTPstands for Certified Red Team Professional and is a completely hands-on certification. It compares in difficulty to OSCP and it provides the foundation to perform Red Team operations, assumed breaches, PCI assessments and other similar projects. Note that the Certified Red Team Professional (CRTP) course and labs are now offered by Altered Security who are creators of the course and labs.
To be certified, a student must solve practical and realistic challenges in a fully patched Windows infrastructure labs containing multiple Windows domains and forests. The certification challenges a student to compromise Active Directory by abusing features and functionalities without relying on patchable exploits. Students will have 24 hours for the hands-on certification exam.
A certification holder has the skills to understand and assess security of an Active Directory environment.
My experience
After three weeks spent in the lab, I decided to take the CRTP exam over the weekend and successfully passed it by compromising all the machines in the AD. I had very limited AD experience before the lab, but I found my experience with OSCP extremely useful on how to approach and prepare for the exam. The practical exam took me around 6-7 hours, and the reporting another 8 hours.
If you want to level up your skills and learn more about Red Teaming, follow along! In this article I cover everything you need to know to pass the CRTP exam from lab challenges, to taking notes, topics covered, examination, reporting and resources.
The Lab
The lab access was granted really fast after signing up (<24 hours). Each student has his own dedicated Virtual Machine where all the tools needed for the attacks are already installed and configured. Connecting to the Virtual Machine is straight forward, as it is possible to use both OpenVPN of the browser.
I consider this an underrated aspect of the course, since everything is working smoothly and students don’t have to spent time installing tools, dependencies or debugging errors . The lab was very well aligned with the material received (PDF and videos) such that it was possible to follow them step by step without issues.
The lab contains around 40 flags that can be collected while solving the exercises, out of which I found around 35. I found that some flag descriptions were confusing and I couldn’t figure it out the exact information they are they asking for.
Support was very responsive – for example I once crashed the DNS service during the DNSadmin attack and I asked for a reset instead of waiting until next day, which they did.
Taking Notes
I recommend anyone taking the course to put the most effort into taking notes - it’s an incredible way to learn and I’m shocked whenever I hear someone not taking notes. In case you need some arguments:
- Notes are a useful record of key information
- Taking notes helps you remember what you heard
- Taking notes helps you to focus and listen effectively
- Selecting what to note down increases your understanding
- Notes create a resource for exam preparation
For each video that I watched, I would follow along what was done regardless how easy it seemed. I took notes for each attack type by answering the following questions:
- what can be achieved with this attack?
- what is the vulnerability/why is this possible?
- how to perform the attack?
- what tools can be used?
- example of commands
- example of success and error messages
Additionally for each attack, I would skim though 2-3 articles about it and make sure I didn’t miss anything. Personally, I’m using GitBook for notes taking because I can write Markdown, search easily and have a tree-structure.
Topics Covered
Overall, I ended up structuring my notes in six big topics, with each one of them containing five to ten subtopics:
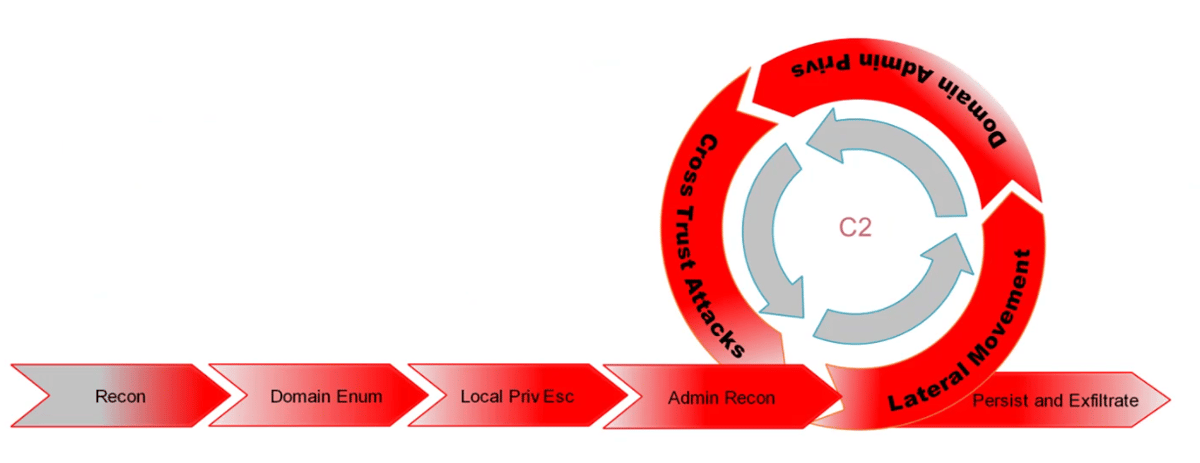
Enumeration - is the part where we try to understand the target environment and discover potential attack vectors. The enumeration phase is critical at each step to enable us to move forward. In the enumeration we look for information about the Domain Controller, Honeypots, Services, Open shares, Trusts, Users, etc.
Lateral Movement - refers to the techniques that allows us to move to other machines or gain a different set of permissions by impersonating other users for example. In this phase we are interested to find credentials for example using Mimikatz or execute payloads on other machines and get another shell.
Bypasses - as we are against fully patched Windows machines and server, security mechanisms such as Defender, AMSI and Constrained mode are in place. This section cover techniques used to work around these.
Persistence - once we got access to a new user or machine, we want to make sure we won’t lose this access. Persistence occurs when a threat actor maintains long-term access to systems despite disruptions such as restarts. The lab covers a large set of techniques such as Golden Ticket, Skeleton Key, DCShadow, ACLs, etc.
Privilege Escalation - elevating privileges on the local machine enables us to bypass several security mechanism more easily, and maybe find additional set of credentials cached locally. Elevating privileges at the domain level can allow us to query sensitive information and even compromise the whole domain by getting access to Domain Admin account.
Defense - lastly, but not last the course covers a basic set of rules on how some of these attacks can be detected by Blue Team, how to avoid honeypots and which techniques should be avoided in a real engagement.
Examination
The students are provided access to an individual Windows environment, which is fully patched and contains the latest Windows operating systems with configurations and privileges like a real enterprise environment.
To be successful, students must solve the challenges by enumerating the environment and carefully constructing attack paths. The students will need to understand how Windows domains work, as most exploits cannot be used in the target network.
I suggest that before the exam to prepared everything that may be needed such as report template, all the tools, BloodHound running locally, PowerShell obfuscator, hashcat, password lists, etc. Don’t forget to:
- Write down each step you perform
- Write down the command + output
- Take screenshot
This will help a lot after you are done with the exam and you have to start writing the report! The last thing you want to happen is doing the whole lab again because you don’t have the proof of your flags, while you are running out of time.
Once the exam lab was set up and I connected to the VM, I started performing all the enumeration I’ve seen in the videos and that I’ve taken notes of. Since I wasn’t sure what I am looking for, I felt a bit lost in the beginning as there are so many possibilities and so much information. It helped that I knew that some of the tools will not work or perform as expected since they mention this on the exam description page – so I went in without any expectation.
After around 2 hours of enumeration I moved from the initial machine that I had access to another user. Afterwards I started enumerating again with the new set of privileges and I’ve seen an interesting attack path. My focus moved into getting there, which was the most challenging part of the exam. I got domain admin privileges around 6 hours into the exam and enterprise admin was just a formality.
Some advises that I have for any kind of exams like this:
- enumerate and review – make sure to have a list of enumeration steps that you want to perform, if nothing interesting shows up, enumerate again: different tools, parameters, strategies. You have 24 hours, don’t rush and don’t get freaked out when you can’t find anything. Finding it is the hardest part, once you have it, the exploitation should be a walk in the park
- take breaks to celebrate – I take a break after every small step that I make, it helped me relax knowing that I’m one step closer to the objective and to think about it in perspective. “What can I do now with the user/box/hash/etc. that I got?”
- don’t overlook, but don’t go into rabbit holes either – when you find something, try it out – don’t assume it doesn’t work until you try. I think it’s a fine line on how hard you should try before moving further, and that comes with experience. Fortunately I didn’t get into any rabbit holes even if it felt there were some red herrings laying around (but could have been as well alternative paths!)
Reporting
I did the reporting during the 24 hours time slot, while I still had access to the lab. I suggest doing the same if possible. I took screenshots and saved all the commands I’ve executed during the exam so I didn’t need to go back and reproduce any attacks due to missing proves. My final report had 27 pages, with lots of screenshots. After I submitted the report, I got a confirmation email a few hours later, and the statement that I passed the following day.
Resources
I know there are lots of resources out there, but I felt that everything that I needed could be found here:
-
https://tripla.dk/2021/01/21/certified-red-team-professional-crtp-by-pentester-academy-exam-review/
-
https://www.ired.team/offensive-security-experiments/active-directory-kerberos-abuse
- https://casvancooten.com/posts/2020/11/windows-active-directory-exploitation-cheat-sheet-and-command-reference/
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Methodology%20and%20Resources/Active%20Directory%20Attack.md#active-directory-attacks
+
*







